Microsoft is rolling out a major Identity Threat Detection and Response (ITDR) update that shifts from account-centric alerts to identity-centric defense, bringing unified sensors, deeper cross-domain correlation, and context-rich investigations to security operations teams using Microsoft Defender for Identity. Authored by Sharon Ben Yosef, Partner General Manager for Microsoft Defender for Identity, the announcement highlights that identities—human and non-human across hybrid and multivendor environments—are now the true perimeter, with more than 7,000 password attacks per second in 2024 and about 66% of attack paths involving identity compromise.
What’s new
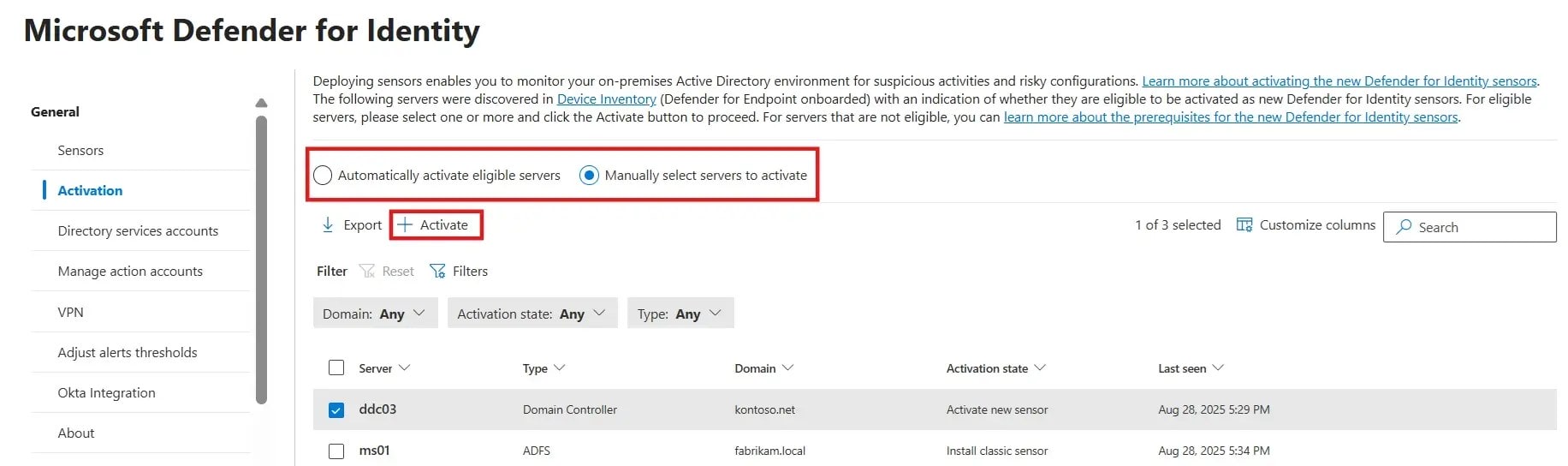
 Microsoft announced the general availability of the unified identity and endpoint sensors first unveiled at Ignite 2024, making it easier for new Defender for Identity customers to activate protections on qualifying domain controllers and immediately gain identity-specific visibility, posture recommendations, alerts, and automatic attack disruption within the Defender experience. The platform now emphasizes an identity-centric view that correlates accounts across on-premises and cloud to reveal a single identity’s true footprint for more accurate investigations and responses.
Microsoft announced the general availability of the unified identity and endpoint sensors first unveiled at Ignite 2024, making it easier for new Defender for Identity customers to activate protections on qualifying domain controllers and immediately gain identity-specific visibility, posture recommendations, alerts, and automatic attack disruption within the Defender experience. The platform now emphasizes an identity-centric view that correlates accounts across on-premises and cloud to reveal a single identity’s true footprint for more accurate investigations and responses.

Defender for Identity deepens native integration with Microsoft Entra ID to provide real-time visibility into identity activity and risk levels, tying directly into Zero Trust policies via Conditional Access and user containment to enforce protections at the policy edge. Because most enterprises run heterogeneous identity stacks, Microsoft also extends ITDR coverage to third-party cloud identities like Okta, offering unified visibility, posture insights, and response across platforms to reduce security blind spots.
Why it matters

Traditional network boundaries have dissolved with hybrid work and cloud-first strategies, making identity signals—and their correlations across domains—critical for early detection and rapid containment of modern attacks. By unifying sensor coverage, correlating identity signals with endpoint and cloud telemetry, and surfacing enriched context directly in the SOC workflow, Microsoft aims to help teams cut through alert noise and block lateral movement faster.
The update explicitly addresses the “seams” that often emerge between identity and security operations by streamlining contextual insights, actions, and workflows so they flow seamlessly across teams and tools without gaps that attackers can exploit. The result is a more cohesive defense that ties identity posture, detection, and response into a single, operationalized picture of a threat as it unfolds.
Microsoft Defender for Identity capabilities
-
Unified sensors: General availability of Defender for Identity’s unified identity and endpoint sensors simplifies deployment and accelerates time to value on qualifying domain controllers, bringing identity protections directly into Defender’s incident and posture experiences.
-
Identity-centric correlation: Signals are correlated across accounts, platforms, and environments to map multiple accounts back to a single identity, improving triage accuracy and response decisions for complex, hybrid threats.
-
Entra integration: Native integration with Microsoft Entra ID adds real-time activity and risk visibility, plus tight linkage to Conditional Access and user containment for Zero Trust-aligned enforcement.
-
Multivendor coverage: Support for third-party identities such as Okta extends unified visibility and ITDR capabilities across heterogeneous environments common in large enterprises.
-
Privileged identity protection: Integrations with Privileged Access Management (PAM) solutions enhance monitoring and protection for high-value identities that are frequent attacker targets.
-
XDR correlation and hunting: Microsoft Defender’s XDR correlations automatically link identity signals with endpoint, application, and cloud insights, while Advanced Hunting exposes relationships across domains to uncover patterns otherwise missed.
-
Operationalized SOC workflows: Identity alerts from Defender and Entra are correlated into broader incidents in Microsoft Defender XDR, posture recommendations appear in Exposure Management, and automatic attack disruption can dynamically contain compromised users, devices, and sessions.
-
Coverage for non-human identities: Protections extend to AI agents, service accounts, and third-party identities, using behavioral signals to detect drift and enforce policy where many tools lack visibility or enforcement reach.
SOC and CISO takeaways
For SOC teams, the biggest lift comes from identity-centric correlation and cross-domain incidenting, which turn fragmented identity signals into actionable, end-to-end narratives with recommended actions and automated containment where appropriate. For CISOs, the expanded posture insights and Exposure Management tie identity hardening into a continuous program that prioritizes privileged accounts, non-human identities, and cross-tenant risks that often lead to lateral movement.
By treating identity telemetry as a first-class signal in incident response—and aligning identity, endpoint, and cloud views—organizations can shorten dwell time and reduce the blast radius of compromised credentials or abused privileges. The inclusion of PAM integrations and multivendor identity support reflects real-world complexity and helps teams close coverage gaps that persist in hybrid environments.
How to get started
New Defender for Identity customers can activate the unified sensor to onboard faster and begin receiving identity-specific visibility, posture guidance, and alerts directly in Microsoft Defender’s unified portal and workflows. Existing customers with current sensors do not need to take action immediately and should watch for migration guidance in the coming months to transition without disruption.
 Microsoft recommends a unified approach between identity and security teams so context, actions, and workflows move seamlessly across groups, minimizing oversights while accelerating triage and response. Teams should also review privileged identity coverage, multicloud and third-party identity integrations, and automatic attack disruption settings to ensure protections align with Zero Trust and organizational risk priorities.
Microsoft recommends a unified approach between identity and security teams so context, actions, and workflows move seamlessly across groups, minimizing oversights while accelerating triage and response. Teams should also review privileged identity coverage, multicloud and third-party identity integrations, and automatic attack disruption settings to ensure protections align with Zero Trust and organizational risk priorities.
Other news happening in the world of Microsoft
With mandatory MFA across Partner Center and APIs converging with a redesigned Security workspace, partners that act now to harden posture, formalize 24‑hour alert response, and adopt least‑privilege patterns will minimize disruption and safeguard CSP standing—see the full breakdown and checklist. For a quick weekend break, check this week’s Xbox Free Play Days lineup for Oct 23–26.
To boost day‑to‑day productivity, explore the new Actions and Journeys in Edge’s Copilot Mode and see how it can streamline routine tasks across browsing and work. And for leaders steering their orgs from systems of record to systems of action, dive into Dynamics 365’s agentic apps, new sales/service agents, and pooled Copilot credits to accelerate outcomes across CRM, ERP, and contact center operations.
The Bottom Line
Microsoft’s update reframes ITDR around complete identity context, stronger cross-domain correlation, and automated, policy-aligned response—capabilities that directly target the most common attack paths and identity-driven risks seen in today’s hybrid environments. With unified sensors now generally available and deeper Entra integration, security leaders can tighten defenses across human and non-human identities while improving SOC efficiency and response precision.
Discover more from Microsoft News Now
Subscribe to get the latest posts sent to your email.
