Microsoft has taken a significant step forward in its ongoing battle against evolving cyber threats by releasing the second installment of its Secure Future Initiative (SFI) patterns and practices library. This update, detailed in a blog post published on October 7, 2025, by Hammad Rajjoub, Director of Security Marketing at Microsoft, builds on the initial launch from August 2025 and provides six new actionable guides designed to help organizations strengthen their security postures.
As cyber attackers grow more sophisticated, these patterns offer practical, practitioner-led advice rooted in Microsoft’s internal implementations, emphasizing principles like Zero Trust to prevent breaches, limit lateral movement, and accelerate threat response. For businesses navigating complex cloud environments, this expansion arrives at a critical time, especially with the impending end of Windows 10 support and heightened scrutiny on supply chain vulnerabilities.
Microsoft Secure Future Initiative
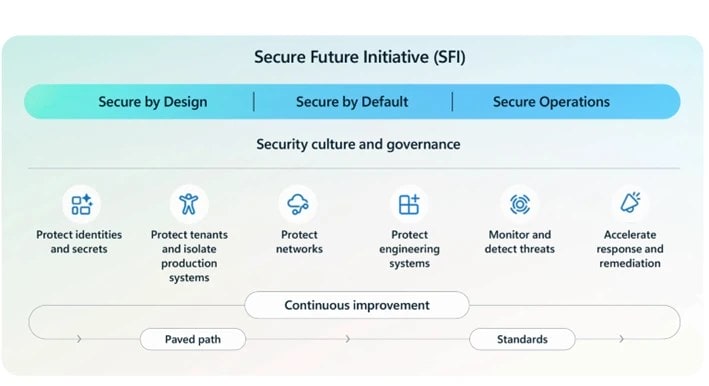
The Microsoft Secure Future Initiative (SFI), launched in November 2023, represents a multi-year engineering effort equivalent to mobilizing over 34,000 engineers to mitigate risks across Microsoft’s vast ecosystem. Guided by three core principles—secure by design, secure by default, and secure in operations—the SFI focuses on six pillars: protecting identities and secrets, isolating tenants and systems, protecting networks, safeguarding engineering systems, monitoring and detecting threats, and accelerating response and remediation.
The Microsoft Secure Future Initiative’s progress reports, including the April 2025 edition, highlight measurable advancements, such as decommissioning over 5.75 million inactive tenants and implementing phishing-resistant multi-factor authentication (MFA) at scale. Now, with this second wave of patterns, Microsoft is sharing deeper insights into how it has operationalized these pillars, enabling customers, partners, and the broader security community to adopt similar strategies. The blog post underscores that these resources are not abstract theories but reusable solutions, akin to software design patterns, tailored to real-world challenges like inconsistent CI/CD pipelines and shadow tenants.

At the heart of this release are six new patterns and practices, each addressing a specific cybersecurity risk with a structured format: a pattern name, problem description, Microsoft’s solution, implementation guidance, and implications. This consistent taxonomy makes the library accessible for security teams, allowing them to quickly identify, understand, and apply fixes without starting from scratch.
The first wave in August 2025 introduced eight patterns covering topics like phishing-resistant MFA and rapid anomaly detection, which have already helped organizations reduce dwell times for threats and standardize secure development. The new additions expand coverage into network protection, tenant isolation, and engineering safeguards, reflecting Microsoft’s learnings from incidents and customer feedback. By making these internal practices public, Microsoft aims to foster a collaborative ecosystem where security is proactive rather than reactive.
- One of the standout patterns is “Network Isolation,” aligned with the SFI pillar of protecting networks. This guide helps organizations contain breaches by default through strong segmentation, such as per-service access control lists (ACLs) and isolated virtual networks. The problem it tackles is the ease of lateral movement for attackers once they breach a perimeter, a common vector in ransomware attacks that have cost global businesses billions. Microsoft’s solution involved implementing granular network controls across its production environments, limiting blast radii and preventing widespread compromise. Guidance includes auditing network traffic, enforcing least-privilege access, and using tools like Azure Virtual Network for isolation, with implications noting potential initial complexity in hybrid setups but long-term resilience gains. For enterprises relying on Azure or multi-cloud architectures, this pattern is particularly relevant as it integrates with Zero Trust models to minimize exposure.
- Complementing network defenses, “Secure All Tenants and Their Resources” focuses on the pillar of protecting tenants and isolating systems. Shadow tenants—forgotten or weakly secured cloud environments—pose a hidden risk, often exploited for persistence or data exfiltration. Microsoft addressed this by applying baseline policies like MFA and Conditional Access to every tenant, retiring unused ones to eliminate blind spots. The guidance recommends inventorying all tenants, enforcing uniform security baselines via Microsoft Entra ID, and automating retirement processes, which can reduce attack surfaces by up to 50% in large organizations. Implications include improved compliance with regulations like GDPR but require ongoing governance to avoid over-retention of resources. This pattern is timely for businesses scaling cloud adoption, as it prevents the “forgotten tenant” pitfalls that have led to high-profile breaches.
- Identity security takes center stage in “Higher Security for Entra ID Apps,” another tenant isolation pattern. Cyber attackers frequently abuse misconfigured Entra ID (formerly Azure AD) applications for cross-tenant attacks, exploiting unused apps or lax permissions as backdoors. Microsoft’s internal fix involved removing redundant apps, tightening permissions, and mandating strong authorization protocols. Practical steps include auditing app registrations, implementing just-in-time access, and using Entra ID’s built-in tools for verification, helping close common gaps that fuel 80% of identity-based incidents. While implementation may involve app refactoring, the trade-offs favor reduced unauthorized access and easier audits. As remote work blurs traditional boundaries, this guide empowers IT admins to secure app ecosystems without disrupting productivity.
- Shifting to engineering systems, “Zero Trust for Source Code Access” ensures only verified developers can commit critical changes, preventing malicious injections. The risk here is supply chain sabotage, where attackers slip code into pipelines, as seen in recent SolarWinds-style incidents. Microsoft enforces proof-of-presence MFA for merges, integrating it with GitHub and Azure DevOps for seamless verification. Guidance covers setting up role-based access controls (RBAC) and automated checks, with implications highlighting faster dev cycles post-adoption despite initial training needs. This pattern is essential for software firms and DevOps teams aiming to build trust into their pipelines.
- “Protect the Software Supply Chain” extends this by governing CI/CD processes and dependencies. Fragmented builds and unvetted packages invite exploits, amplifying risks in production. Microsoft’s approach uses standardized templates, internal feeds, and automated scanning via tools like Dependabot and Azure Pipelines. Recommendations include SBOM generation and vulnerability gating, reducing supply chain attacks by enforcing traceability. Trade-offs involve pipeline standardization overhead, but outcomes include blocked threats before deployment. With rising nation-state targeting of supply chains, this pattern positions organizations for resilient development.
- Finally, “Centralize Access to Security Logs” bolsters monitoring and threat detection. Decentralized logs slow investigations, allowing threats to linger. Microsoft centralized collection with extended retention in Azure Sentinel, enabling unified visibility across clouds. The guide advises standardizing formats, using SIEM tools for aggregation, and setting retention policies compliant with NIST standards. Implications include quicker MTTR (mean time to response) but higher storage costs, offset by AI-driven analytics. In an era of fast-moving attacks, this pattern accelerates SOC efficiency.
These patterns are accessible via the dedicated Secure Future Initiative webpage, where users can download full articles and explore the growing library. A new SFI video on Microsoft’s Trust Center site (https://www.microsoft.com/trust-center/security/secure-future-initiative) features leadership discussing the “security above all” ethos. The April 2025 progress report (available at https://cdn-dynmedia-1.microsoft.com/is/content/microsoftcorp/microsoft/final/en-us/microsoft-brand/documents/sfi-april-2025-progress-report.pdf) provides metrics on SFI’s impact, such as 99% network device logging and reduced vulnerability exposure times. Microsoft encourages organizations to consult account teams for roadmap integration and follow updates on the Security Blog (https://www.microsoft.com/en-us/security/blog/).

This expansion of Secure Future Initiative patterns highlights Microsoft’s leadership in cybersecurity, especially as IDC named it a Leader in Worldwide Extended Detection and Response (XDR) Software for 2025. By sharing these battle-tested Secure Future Initiative practices, Microsoft not only elevates its own defenses but equips the industry to combat threats like those exploiting Microsoft Teams or legacy Windows systems. For msftnewsnow.com readers, adopting these could mean the difference between breach prevention and costly recovery. As Hammad Rajjoub notes, security is a shared journey—let’s build a secure future together. With more releases planned, the Secure Future Initiative (SFI) library promises to evolve alongside threats, offering a blueprint for resilient digital operations in 2025 and beyond.
Discover more from Microsoft News Now
Subscribe to get the latest posts sent to your email.
